Last updated: November 14, 2024
JumpCloud
An Identity Provider (IdP) vouches for the identity of a person through the use of an authentication token. Virtual Appliance uses IdP for several things, including logging in to the Admin Console and portals, deploying printers, releasing print jobs, and more.
If you use an IdP, the Control Panel Application (CPA) only supports badge and PIN authentication.
Configure JumpCloud
To add an app integration for the Virtual Appliance connection do the following:
- Create JumpCloud App.
- Add IdP Template.
- Configure Single Sign On.
- Add the X509 Certificate.
- Complete IdP Settings.
- Configure Provisioning.
- Add Virtual Appliance Admins.
1. Create JumpCloud App
Open a browser and log into your JumpCloud Administrator Console. (console.jumpcloud.com/login/admin).
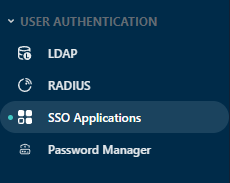
- Expand the User Authentication option in the left-side menu.
-
Select the SSO Applications option.
- Select the + Add New Application button.
- Search for PrinterLogic, and select the PrinterLogic SaaS application.
- Select the Next button.
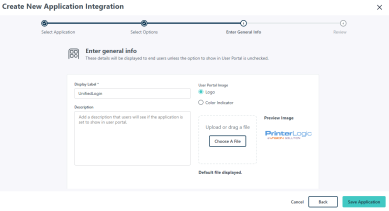
- In the Display Label field, name your app.
- (Optional): Add a description and upload a logo.
- Select Save Application.
- Select Configure Application.
Leave the current browser open to the new app page. To continue the app configuration, you need to open another browser and open the and access the service provider information.
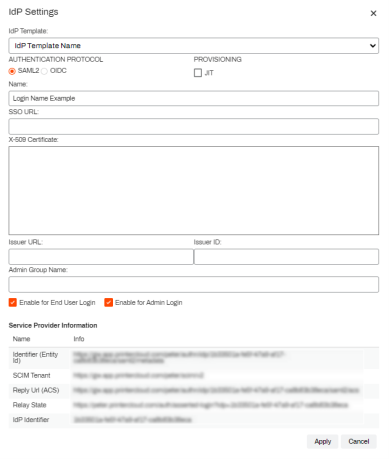
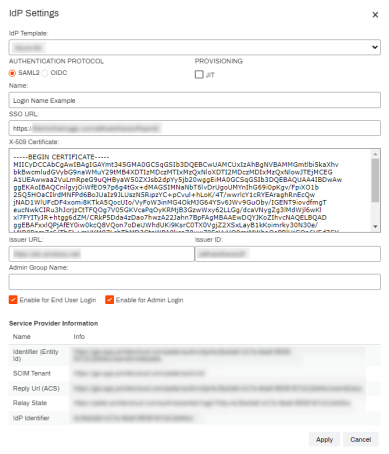
If the IdP Settings page does not look like the image shown below, you may not be using the latest version and should contact Product Support to upgrade your IdP settings.
2. Add IdP Template
- In a separate browser tab, open your Virtual Appliance Admin Console and sign in.
- Select Tools
 Settings
Settings  General, and scroll down to the Identity Provider Settings section.
General, and scroll down to the Identity Provider Settings section. - Select IdP, and then select Add.
- Select the identity provider you want to configure in the IdP Template drop-down.
- Select SAML2 in the Authentication Protocol section.
-
For Provisioning it is assumed that JIT will be used for most Virtual Appliance applications. Check the box for JIT provisioning.
When you consider how to set up your IdP configuration be aware that SCIM provisioning requires an open connection from the IdP provider into the Virtual Appliance instance gateway container. We recommend JIT provisioning when setting up your IdP connection.
- In the Name field, enter the name you want displayed on the login button for users, e.g. My Company, Login, Acme Corp, etc.
- Scroll down and select the desired enable setting(s).
- Enable for End Users Login — Allows end users to login using this IdP. (Self-service Portal)
- Enable for Admin Login — Allows Admin users to login using this IdP. (Admin Console)
- Both boxes can be checked when using a single IdP, or if the admin and end users use the same IdP to log in.
Keep the IdP Settings screen open so that the Service Provider Information at the bottom is available for the following steps.
3. Configure Single Sign On
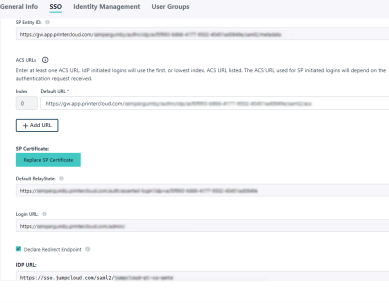
- In the JumpCloud app, select the SSO tab.
-
In the IdP Entity ID field enter the following URL.
Copy Codehttps://jumpcloud.com/<your_IdP_ID> - Copy the IdP Identifier from the Virtual Appliance Admin Console Service Provider Information section and replace the <your_IdP_ID> portion of the IdP Entity ID URL with the identifier.
- Back in the Admin Console IdP Settings page, enter https://jumpcloud.com/ in the Issuer URL field.
- Under the Service Provider Information section, copy the IdP Identifier and paste the value in the Admin Console Issuer ID field.
- In the IdP Settings window, copy and paste the following into the JumpCloud SSO tab:
- Copy the Admin Console Identifier (Entity Id) and paste the value into the JumpCloud SP Entity ID field
- Copy the Admin Console Reply Url (ACS) and paste the value into the JumpCloud ACS URLs Default URL field.
- Copy the Admin Console Relay State and paste the value into the JumpCloud Default RelayState field.
- In the JumpCloud Login URL field, replace the “YOUR_SUBDOMAIN” portion of the URL with your instance subdomain.
- Check the Declare Redirect Endpoint box.
- Copy the IDP URL in JumpCloud, and paste this into the Admin Console SSO URL field.
-
Scroll down to the Attributes section and configure mappings as needed.
For more information about the SSO Connector fields in JumpCloud see SSO Application Connector Fields.
4. Add the X-509 Certificate
- Scroll up to the JumpCloud Metadata section in the app's SSO tab, and select the Export Metadata button.
- Open the XML file with a text editor, like Notepad++.
-
Remove the export content before and after the X-509 Certificate.
Ensure you are copying only the X-509 certificate content from the text editor. This is the section between the > and < characters as shown in the image. The rest can be removed.
-
Add the following headers before and after the X-509 Certificate content.
Copy Code-----BEGIN CERTIFICATE-----Copy Code-----END CERTIFICATE----- - Copy the X-509 Certificate with the adjusted headers.
- Return to the Admin Console IdP Settings window and paste the certificate into the X-509 Certificate field.
- Select Apply in the Admin Console.
- Select Save in the Admin Console.
- Select Save in JumpCloud.
5. Complete IdP Settings
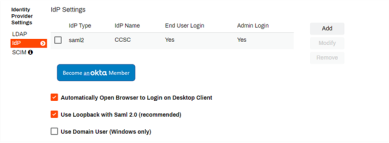
- On the Admin Console General page, navigate back to the Identity Provider Settings section.
-
To have Virtual Appliance prompt your users to authenticate through the IdP when performing any function requiring authorization, such as installing a printer, select the Automatically Open Browser to Login on Desktop Client option.
If this option is not selected, the user must manually navigate to the IdP login screen to sign in.
-
We recommend enabling the Use Loopback with SAML2 option. The IdP needs to provide an authentication token to the desktop clients whenever authentication happens. This option allows the client to handle the token and automatically log in without interaction from end users.
- The option to Use Domain User (Windows only) will automatically authorize domain-joined Windows users and not require login via the configured IdPs.
- Select Save in the top-right corner of the General page.
6. Configure Provisioning
The provisioning steps vary depending on whether you are using SCIM or JIT provisioning. Please choose the appropriate option below to view the corresponding steps for the method you are using.
SCIM Provisioning
Enable SCIM Provisioning
These steps are only for the JumpCloud SCIM configuration.
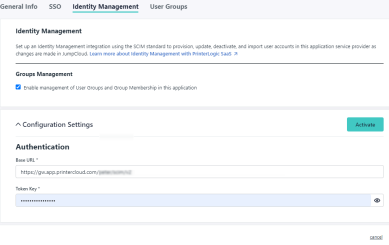
- In the JumpCloud app, select the Identity Management tab.
- Select Configure.
- Check the box for Enable management of User Groups and Group Membership in this application.
- In the Virtual Appliance Admin Console, select the IdP and then select Modify.
- In the Admin Console IdP Settings window, copy the SCIM Tenant URL.
- Paste the SCIM Tenant URL into the JumpCloud Identity Management tab's Base URL field.
- Select Apply in the Admin Console.
- Select Save in the Admin Console.
For more information about SCIM identity management in JumpCloud see Custom SCIM Identity Management.
Generate SCIM Token
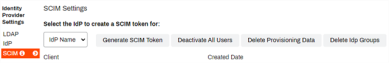
- In the Virtual ApplianceGeneral settings, select the SCIM option in the Identity Provider Settings section.
- Select your IdP configuration in the drop-down menu.
-
Select Generate SCIM Token.
Generating a SCIM token invalidates any previous tokens for that IdP.
- Select Proceed.
- Copy the token, close the modal, and select Save at the top-right corner of General settings.
- Paste the token into the JumpCloud Identity Management tab's Token Key field.
- Select Activate in JumpCloud.
- Select Save in JumpCloud.
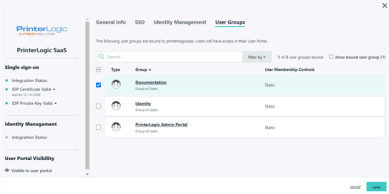
Add User Groups
JIT Provisioning
If you wish to use JIT Provisioning, make sure the JIT option in the IdP Settings modal is checked and do not enable SCIM. Doing so will create duplicate users and impact login and user authentication.
JIT does not support the provisioning of group membership associations, so you cannot apply RBAC roles, printer deployments or portal security roles to groups. All assignments have to be done individually for each user.
When using JIT Provisioning, the application creates users during the first sign-in attempt.
- Access your Virtual Appliance instance and select Sign in with <IdP Name>.
- Attempt to login with your IdP credentials.
-
This login attempt will fail and return you to the login page.
This is expected. With JIT, this action triggers the user creation in the instance.
- The following login attempt with valid credentials initiates a typical login sequence.
Administrators who need access to the Admin Console still need to be added to the Tools ![]() Users page using the steps in Admin Console Users.
Users page using the steps in Admin Console Users.
7. Add Virtual Appliance Admins
For steps on assigning users and roles to the Virtual Appliance Admin Console reference Admin Console Users.
-
New Mobile App Release
iOS: November 11th, 2024 -
Released: November 11th, 2024
-
Released: October 22nd, 2024
Updated Application Version Included